One of the available features we have in office 365 is the “data loss prevention” DLP, which helps us to protect our sensitive information by creating DLP policies in Office 365 and get delve information about what’s going on over email traffic into our organizations, inside and outside. DLP is a known is a familiar concept in the IT field, pretty sure ןא exist in any normal security system, whether in your Firewalls or Anti-Virus.
You can use on DLP also for One Drive for business, that is a great feature for one drive, mainly while users used to share files inside and outside, and if some of them shared corporate content externally you definitely can trace it and prevent it.
Therefore I would like to show you how we can create and make us of DLP in Office 365, let’s start.
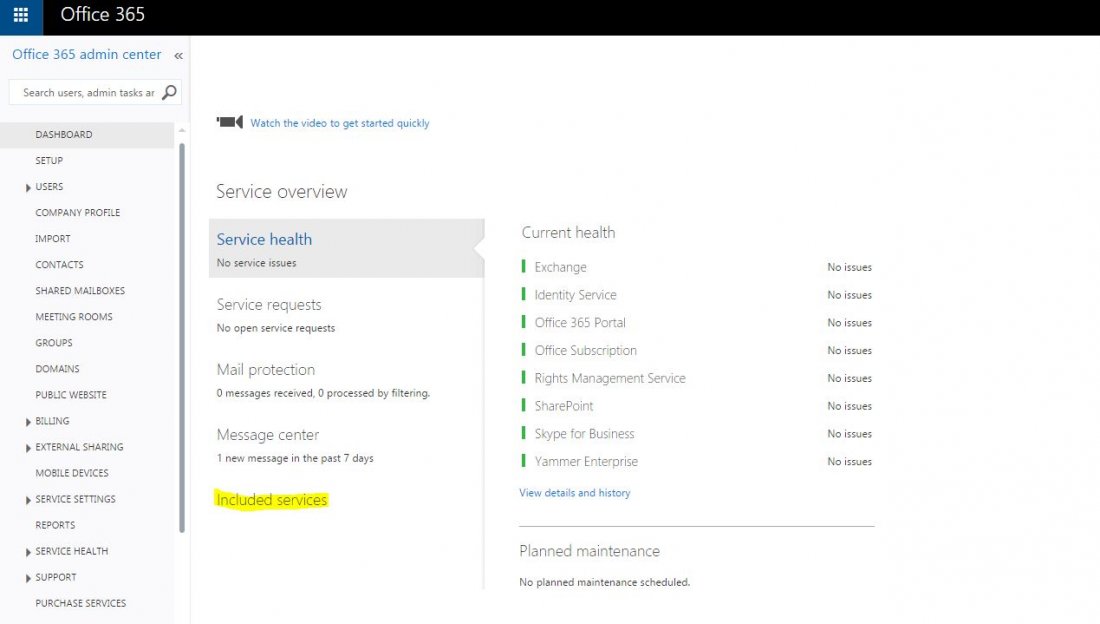
In the office 365 management console navigate to “Compliance management”, and over there you can see the “Data loss prevention” option, click on it and then click on “+”

You can see that we have three available options, let take a look at them:
The first one is “New DLP policy from template“:
By Microsoft Docs, Office 365 includes over 40 ready-to-use templates each one of them describes different detections, for example, I chose the “Israel Personally Identifiable Information (PII) Data 15.0.3.0″ which knows to detect the presence of information commonly considered to be personally identifiable information (PII) in Israel, like national ID number.
So you can use them, go over the templates, you’ll be interested in one of them.

The second option is “DLP policy from a custom template“: we can find some available templates over the Internet which are compatibles to office 365 and add them to here and then use them, no so useful but good to know.

The third option is “New custom DLP policy” which is pretty common because you customize it.
This option allows us to customize DLP policy with your conditions, action, and rules, basically, you define what do you want to prevent.

Edit the “Custom DLP policy”:

You can use on default rules or create new rules I choose on:
Block message with sensitive information:

*Apply this rule if… Outside.
Click on Select sensitive information type:

Click on + and then add the Israeli ID and IP Address:

Here is our sensitive information type- IP and Israeli ID:

Send the report to Meir Peleg:

Let’s send an email to the external recipient with a content of some IP address:

Results:

The report:

The block action works like charm:

Note: All users within the scope of this DLP policy must be licensed on Exchange Online Plan 2 or have an Exchange Enterprise Client Access License (CAL).